global ransomware attack
Posted on by Christian HendrixA global ransomware attack is holding thousands of computers hostage.
Banks, telephone companies and hospitals have all been ensnared in the worldwide hack, with the malware locking down computers while demanding a hefty sum for freedom.
The attack has hit thousands of computers across China, Russia, Spain, Italy and Vietnam, but hospitals in England have attracted the most attention because lives are at risk while hospital systems are locked down. As of Sunday morning, more than 100,000 organizations in at least 150 countries had been affected, according to Europol, the European Union’s police agency.
The spread of the attack was temporarily halted Friday night when a UK cybersecurity researcher inadvertently activated a “kill switch” in the malware’s code, said a Guardian report. That gave US firms additional time to patch their systems to avoid infection, but the researcher said his fix would eventually be sidestepped by the hackers, and it didn’t help networks already hit by the ransomware.
Among them were IT systems and phone lines in National Health Service hospitals in the UK. The East and North Hertfordshire NHS trust updated its website shortly after the attack, telling visitors that they were “currently experiencing significant problems with our IT and telephone network.”
“The investigation is at an early stage but we believe the malware variant is Wanna Decryptor,” the NHS said in a statement Friday.
Avast detected up to 52,000 attacks from the WanaCrypt0r 2.0 ransomware, also called the WannaCry ransomware, yesterday. The majority of the new malware was targeting Russia, Ukraine and Taiwan, Avast Threat Lab team lead Jakub Kroustek said.
The malware had spread across 74 countries as of Friday. On the Malware Tech blog’s tracker, cybersecurity researchers showed that more than 70,000 computers had been affected by the ransomware.
The UK’s National Cyber Security Centre, the Department of Health and NHS England were working to support hospitals that had been affected. IT systems were shut down to prevent the virus from spreading further throughout networks. Hospitals were discouraging people from visiting unless they needed emergency treatment.
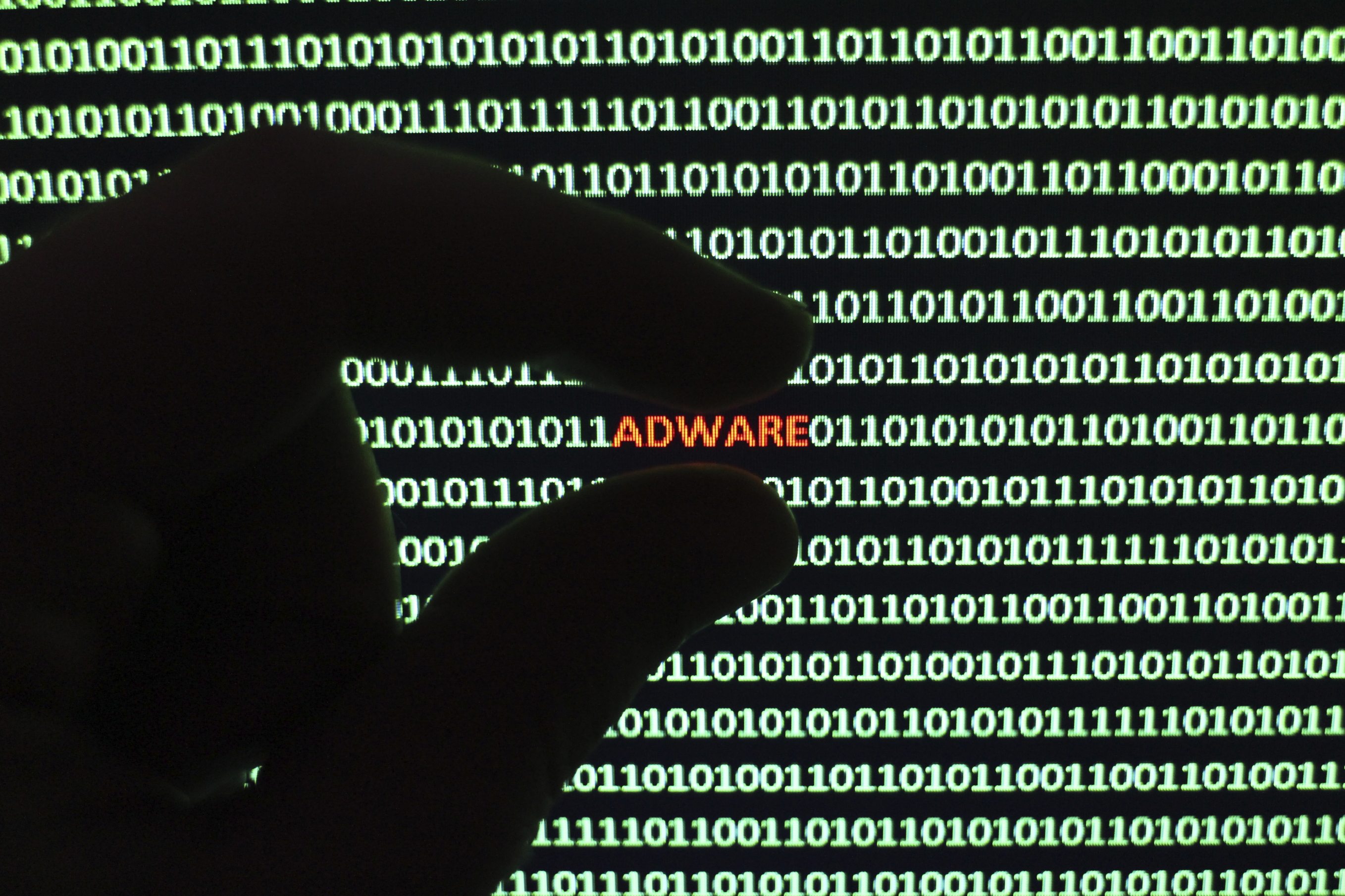
Ransomware is malware that encrypts important files, essentially locking people out of their computers unless they pay up to prevent their entire system from being deleted. Attacks of this kind have spiked in the last year, jumping from 340,665 in 2015 to 463,841 in 2016, according to Symantec. The health care industry has become a major target, with ransomware making up more than 70 percent of malware attacks against hospitals, pharmacies and insurance agencies.
The ransomware is holding each computer hostage for $300 in Bitcoin (roughly £230 or AU$400). The malware demands that hospitals pay by May 15, or all the encrypted files will be deleted by May 19, according to cybersecurity firm Foursys. The firm manages cybersecurity for 140 of the NHS’ hospitals.
“Maybe you are busy looking for a way to recover your files, but do not waste your time. Nobody can recover your files without our decryption service,” the Wana Decrypt0r 2.0 malware threatened.
The NHS said Friday that no private patient data had been stolen. Andy Wool, Foursys’ marketing director, said it wasn’t a targeted attack on the NHS but an exploit that took advantage of the NHS system’s vulnerability. The same ransomware hit Telefonica in Spain.
“Emergency operations may have been cancelled, and automated systems that help monitor in- and outpatients could be affected as well,” Wool said. “It is all hands on deck to try and stop the spread.”
The ransomware uses a vulnerability on Microsoft’s older systems. The company patched the issue in newer systems in March, but many of the NHS’ computers were running on Windows XP, Wool said. Microsoft released a special security update for older systems on Friday.
The exploit was first discovered by the National Security Agency, whose hacking tools were leaked by a group called the Shadow Brokers.
The NSA didn’t respond to requests for comment.
Multiple hospitals in the NHS Trust relayed the same message across social media, advising people against heading to hacked facilities while they were suffering from IT problems.
In a statement Friday from the NHS Merseyside’s information management and technology services, the trust said there had been a “suspected national cyberattack.”
“We just don’t understand the mentality of some people. The only people suffering are people that need emergency care,” NHS staff wrote in a tweet.
As of 3:30 p.m. local time yesterday, up to 16 hospitals had been affected by the ransomware, according to the NHS.
The ransomware has hit hospitals in London, Blackburn, Nottingham, Cumbria and Hertfordshire, according to the BBC.
The Lancashire Post reported that hospitals were using pen and paper to record medical notes for the time being.